Fix AI API Rate Limits: 2026 Guide to Stable API Calls & Residential IP Risk Control
Introduction: It’s Not the API; It’s Your "Trust Score"
In the process of developing AI applications, many teams encounter a strange "periodic collapse": initial calls are smooth, followed by sporadic 429 (Too Many Requests) errors, and eventually, frequent rate limiting or bans even at low concurrency.
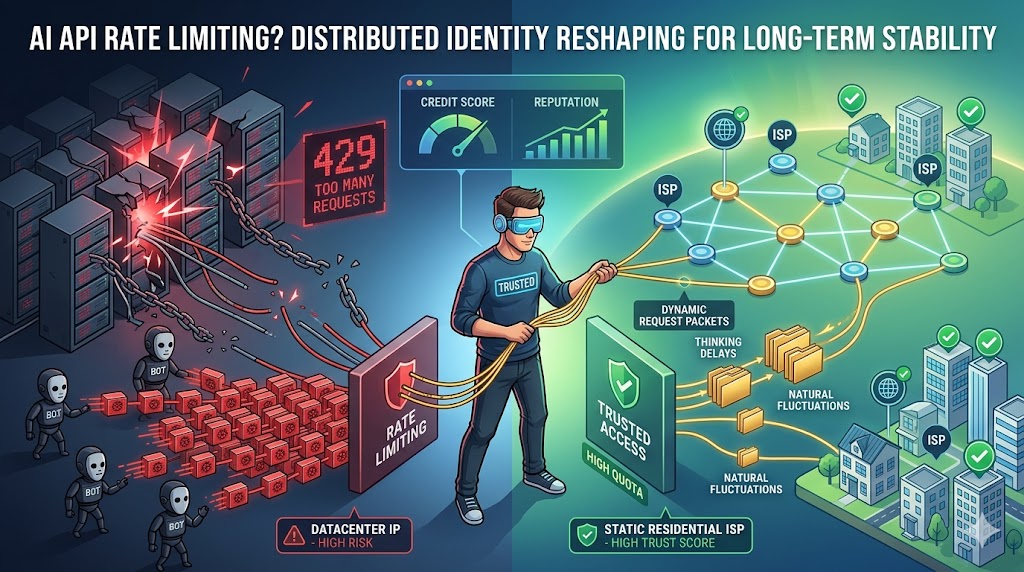
The first instinct for most developers is to check code logic or add retry mechanisms, but the effect is often negligible. In the eyes of risk control systems like OpenAI, Claude, or Google Vertex AI, what is being restricted is never your "request frequency," but your "Caller Identity." Once your identity is flagged as "high risk," any technical code optimization is merely building on quicksand.
I. Unmasking AI Platform Risk Control: Why Are You "Blacklisted"?
1. The Identity Weight Model: How Platforms Scrutinize You
Mainstream AI platforms run sophisticated traffic monitoring systems designed to separate "authentic business traffic" from "malicious abuse/bot traffic." Judgment is no longer based solely on QPS, but on a multi-dimensional weight combination:
- IP Reputation: IPs from Datacenters carry the lowest weight, as they are typically associated with automated scripts and bulk behavior.
- Fingerprint Consistency: Whether TLS fingerprints and HTTP header characteristics match the declared device environment.
- Behavioral Entropy: Is the call interval too precise? Does the request distribution align with the logic of a real human user?
2. Why "Changing IPs" Fails
Simply switching IPs only provides temporary relief. If your operational pattern remains unchanged, the new IP will quickly be associated with your old high-risk tag. This is why many teams feel they are "banned faster with every new IP"—because your behavioral traits have already given you away.
II. Three Hidden Faces of Call Restrictions
1. Soft Throttling: The Invisible "Speed Bump"
The system won't disconnect you immediately but will artificially increase latency or randomly drop packets during concurrency peaks. This usually means your IP segment has entered an "observation period," where the system suppresses performance to test your true intent.
2. Response Degradation: Hidden Quality Drops
This is an extremely subtle restriction. The platform may maintain the connection, but the quality of the returned tokens drops significantly (e.g., incoherent logic or extreme brevity). This indicates your identity has been downgraded to a lower-priority compute cluster.
3. Permanent Flagging: Multi-dimensional Correlation
When dimensions such as IP, payment info, and calling patterns trigger thresholds simultaneously, the account is permanently banned. At this stage, no amount of code adjustment will restore high-priority access to that network environment.
III. The Expert Solution: From Single-Point Requests to "Distributed Identity Reshaping"
The core of evading restrictions lies in reshaping your calling "persona" to look like a globally distributed, authentically growing business entity.
1. Decentralized Traffic Distribution Architecture
Don't funnel all API requests through a single exit point.
- Geographic Polymorphism: Deploy edge relay nodes in different regions based on service node distribution.
- Dynamic Load Weighting: This isn't just for load balancing; it’s for "credit risk" diversification. Ensure the request pattern of a single exit point stays within "natural fluctuation" ranges.
2. IP Strategy: Why Static Residential ISPs are the Only Long-term Fix
In the "class system" of network environments, Residential ISP IPs sit at the top of the trust pyramid.
- The Datacenter Flaw: Sequential IP ranges and public attributes make them easy targets for risk control.
- Residential Trust Endorsement: Originating from real home broadband, these IPs come with authentic geographic coordinates and ISP tags. For AI calls, this simulates requests from "real users around the world," significantly raising the risk control threshold.
IV. Advanced Setup: Building Enterprise-Grade Stability with InstaIP
For technical teams requiring high-frequency calls, underlying network stability is paramount. InstaIP solves more than just connectivity; it mends the "trust gap."
1. Exclusive Fixed Exits to Accumulate "Credit Scores"
InstaIP provides pristine Static Residential IPs, ensuring your calling environment is exclusive.
- Zero "Bad Neighbor" Risk: You don't have to worry about your account being flagged due to the violations of other users on the same network segment.
- Stable Trust Chain: Long-term, consistent use of the same high-quality IP allows AI systems to "get used to" your access, resulting in higher Quota allocations and better stability.
2. Authentic Behavioral Simulation
Leveraging InstaIP’s global residential nodes, developers can achieve a more natural calling curve:
- Eliminate Mechanical Traits: Incorporate random jitter into delays to simulate human thought and operation gaps.
- Environment Logic Closure: Ensure IP geolocation perfectly aligns with the language and time zone configurations in your request headers.
V. Pitfall Guide: Fatal Details That Trip Up Experts
- The Self-Destruction of Invalid Retries: Retrying immediately and frequently after a 429 error only accelerates the system's determination of an attack. Always use an Exponential Backoff algorithm.
- Neglecting TLS Fingerprints: If you use outdated request libraries, their fixed TLS fingerprints are easily identified. Use modern libraries with HTTP/2 support and fingerprint obfuscation.
- Mixed Environment Pollution: Strictly avoid mixing API call traffic with high-risk traffic like scrapers or crawlers within the same proxy pool.
Conclusion: Stability is an "Infrastructure" Marathon
A truly mature AI calling system requires more than ingenious prompts and algorithms; it needs an indestructible underlying environment. When your requests have stable physical origins, high-quality residential identities, and natural behavioral logic, "restrictions" will no longer be an obstacle—they will be your competitive moat.
Testing Recommendation (Critical Step)
Before full deployment, run a real-world test:
A free traffic package is currently available to help you verify:
- How different IPs affect success rates
- Whether rate limits are triggered
- Long-term stability of API calls
In most cases, one test run will give you clear answers.
